The market for decentralized identity is growing—and the key to that growth is to start simple, Indicio.tech’s CTO Ken Ebert, tells KuppingerCole Analysts.
When beginning the journey toward decentralized identity deployment, “The simpler the system you make, the more likely you are to be successful.”
So said Indicio.tech Chief Technology Officer Ken Ebert in a recent presentation to the leading European information security firm KuppingerCole Analysts.
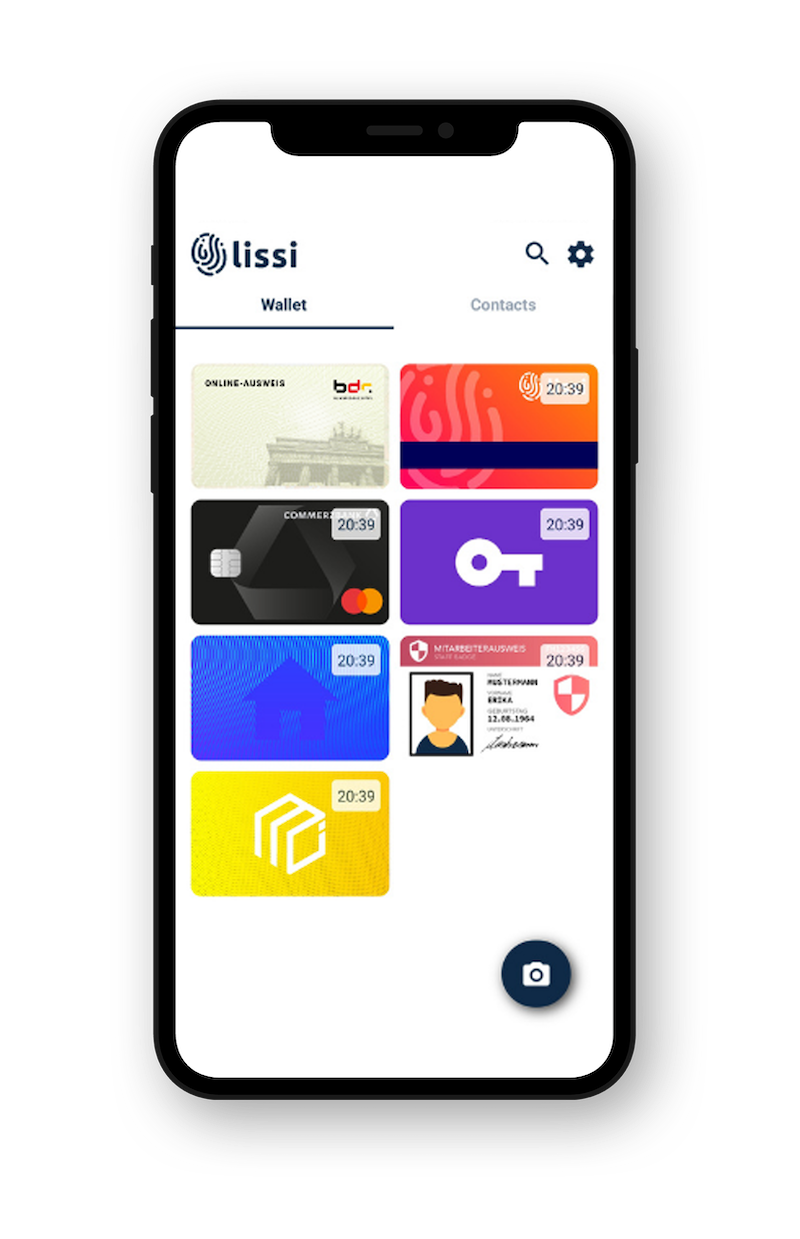
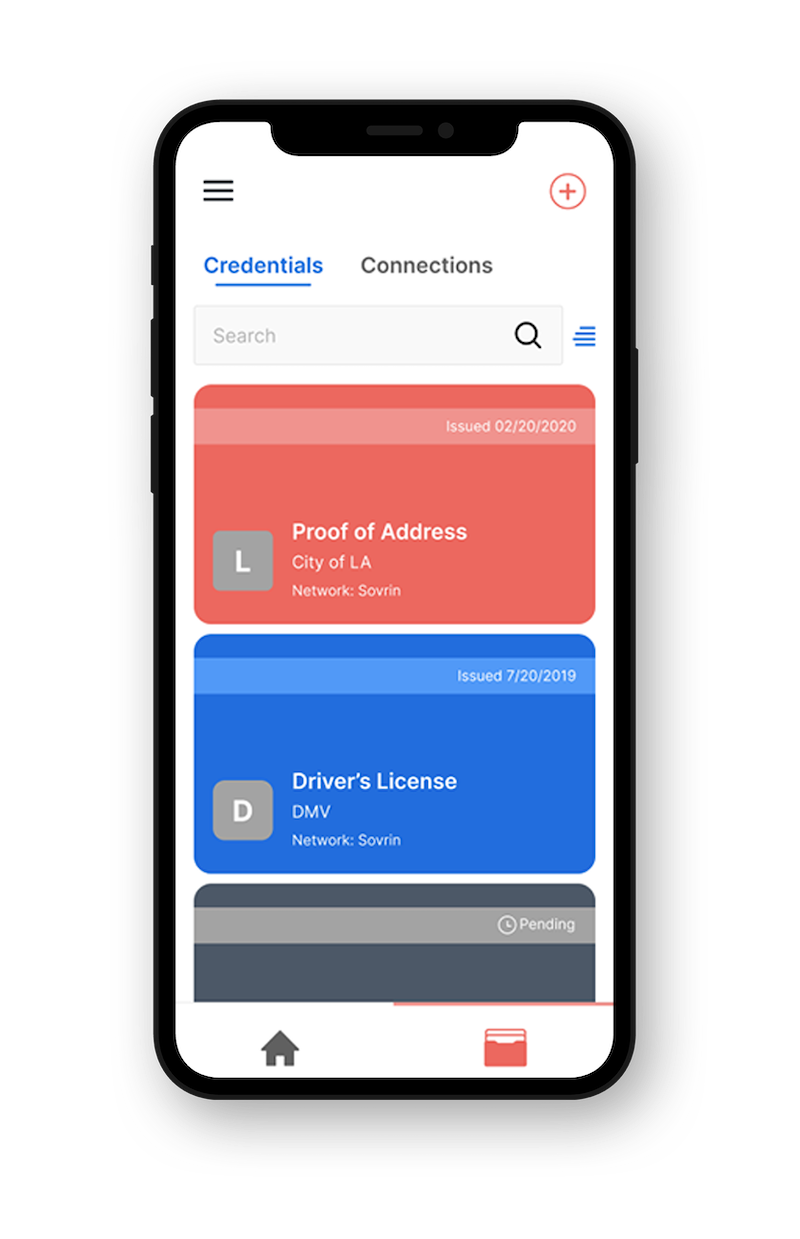
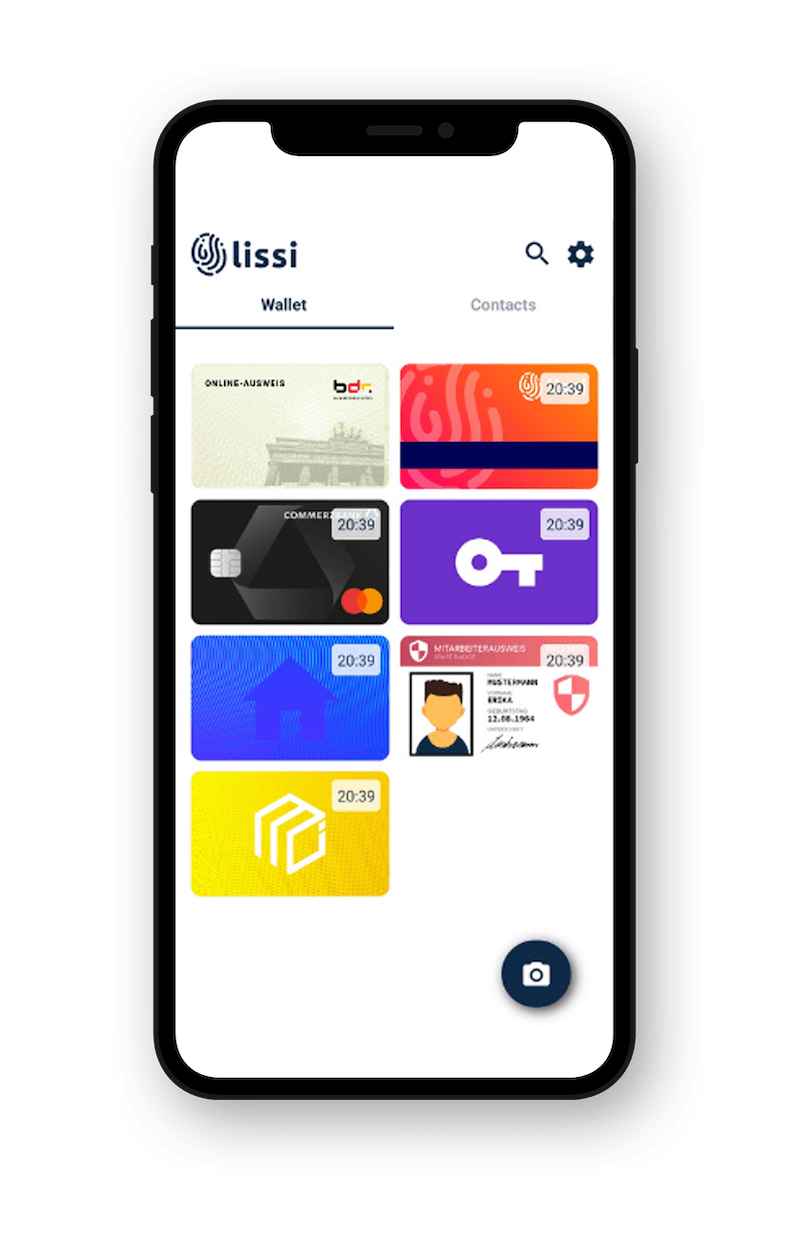
In a simple deployment of decentralized identity, the relationship between credential issuer, credential verifier, and credential holder is already established. Because participants are determined by these relationships, we call this decentralized identity deployment a closed ecosystem. This allows for an iterative implementation in a controlled credential environment versus the chaos that can ensue with a larger scale roll-out.
Oftentimes the implementation of decentralized identity is viewed solely as a purely technology solution, but in reality, the technology solution is just one leg of a three-legged stool:
- One leg does consist of the technology solution— the credential issuer, verifier and holder and the ability to write cryptographic messages to a digital ledger and retrieve them.
- Another is the business solution, namely, what is the problem that decentralized identity is working to solve? Who are the users and what is the benefit? How does it get funded?
- Finally, there is the governance solution, how do users get and use their credentials? How does a digital identity deployment comply with the ever-expanding global regulations on data stewardship?
In the case of a company call center, for example, credentials could be issued to a firm’s customers to speed transactions. If customer service can verify customer credentials in five seconds instead of 30, then that savings can be used to fund the continued adoption of decentralized identity. The technology serves to solve the business problem, and the governance is the closed ecosystem of the firm and its customers.
Not to be overlooked, Ebert says, is the role of marketing, both internal and external to ensure success. This includes at the most basic level communicating to users the pain points that decentralized identity will alleviate and hence its value proposition.
The bigger picture, said Ebert, is that marketing colleagues can help document messaging, synchronize press releases and announcements, and educate across the organization the benefits of decentralized identity.
During the course of an initial decentralized identity roll-out, new and expanded applications of the technology and process improvements will emerge. But again, Ebert stressed that expansion should proceed incrementally. The potential steps here are, going back to our call center example, increasing verifiers, issuers and credential holders to encompass more participants in the firm’s supply chain to decrease friction in performing routine transactions.
Decentralized identity is such a transformative technology it’s easy to get lost in building a new world, rather than building something small, fixing one problem at a time, and learning how to expand from that experience. Simple deployments mean you get to fix actual problems in a way that drives buy-in from stakeholders. Try to boil the ocean of decentralized identity, and you risk getting burned.
Indicio.tech is committed to being a resource hub for decentralized identity, providing enterprise-grade open source tools to get our clients, and the community, building solutions today. By providing Private Networks, the Indicio TestNet, and a variety of customizable training programs, companies and organizations from diverse industries around the world rely on Indicio.tech for expertise in building and scaling their decentralized identity solutions.