New technology is transforming how we think about identity online, how we verify who we are, how we share information, and who should control our data. Gathered under the concept of decentralized identity, all these technologies—blockchains, zero knowledge proofs, decentralized identifiers—offer tremendous opportunities for consumers, businesses, NGOs, and governments.
While it’s easy to get excited by all this (and at Indicio.tech we are very excited), we still have to integrate all these technologies into our current systems for running the world. How do we do this—what are the rules that are going to govern their adoption and use so that these technologies can be trusted?
To manage the identity revolution, a new organization launched last week called theTrust over IP Foundation. Housed at the Linux Foundation, the name plays off one of the most significant technological developments in modern history: The TCP/IP stack.
These are the layered protocols and tools that enable computers on different networks to communicate with each other instantaneously, and which—drum roll—enabled the internet to take virtual flight.
The analogy suggests that trust is something that can be structured like TCP/IP through combining a series of protocols and tools across different technology layers with a series of governance documents. This fusion of governance and technology, says the ToIP Foundation, will create a path towards a trustworthy universal, interoperable system for decentralized identity.
Why the emphasis on governance when blockchains freed us from having to trust in other humans? The reality is that trust is experienced as a human construct and not as a mathematical one; it’s created by and between humans—at least for the present. One could say that ToIP effectively means “trust in identity technology over governance frameworks,” and, perhaps, if all these frameworks align and do their job, and we figure out how to implement machine readability for some of the protocols, trust will come to be seen as instantaneous and “stack-like” as TCP/IP.
The ToIP model
This is the outline structure the ToIP Foundation says we need in order to make sense of the interlocking elements of decentralized identity.
Layer 1, the base, consists of the “utility” networks that provide the “pipes” for credential exchange. Layer 2 deals with the how to communicate using these pipes in a person to person context. Layer 3 establishes trust in the cryptographic communication established in Layer 2 through the exchange of verifiable credentials.. And layer 4 is the kind of ecosystem that can emerge from layers 1 through 3, including Internationally recognized digital passports, privacy preserving age verification, and the streamlining of user-controlled personal information sharing with service institutions.
Overview of the layers
Layer 1 in the stack consists of the networks that enable the use of decentralized identifiers (DIDs), like Sovrin. ToIP envisages that there will be many such utilities as the DID method can be supported by any blockchain, along with those designed for such purposes by Hyperledger Indy.
The ToIP governance stack requires the utility to make its governance authority and framework transparent, along with the identities of those who operate the nodes, and its data protection, privacy, and security policies. The network layer is the engine for running verifiable digital credentials; though ordinary people will never directly interact with it, they must be able to trust that it works.
The key elements of utility governance are the rules for:
- Operating a node
- Authoring a transaction
- Endorsing a transaction
The question you should be asking is, “how do I trust the network utility—the anchor layer for credential exchange? What information do I need?”
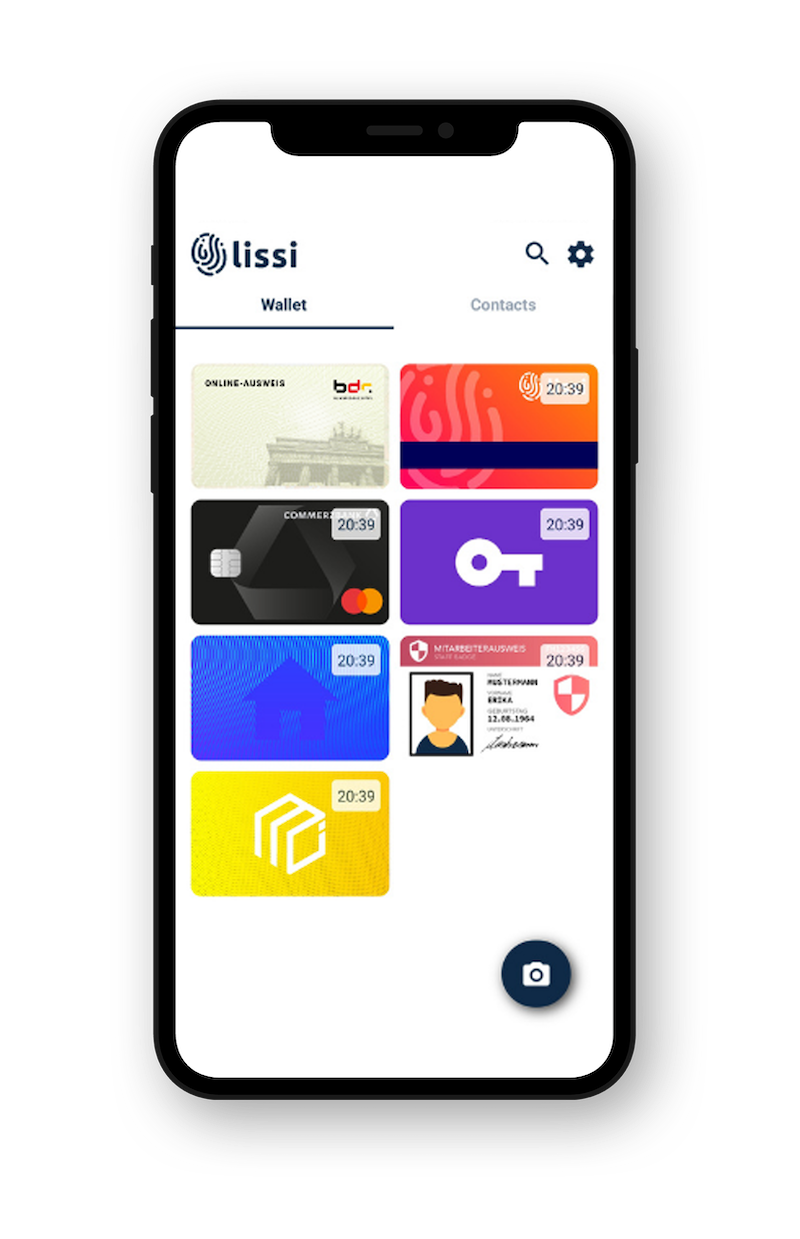
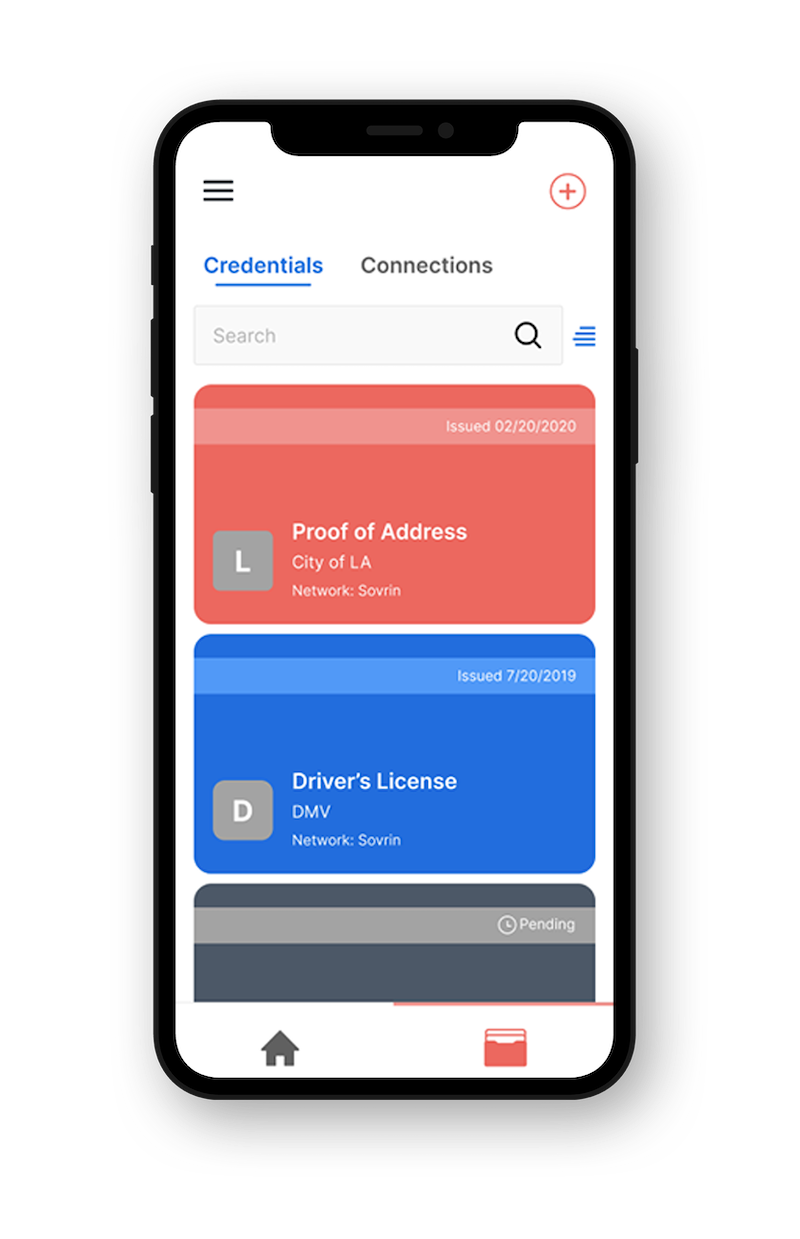
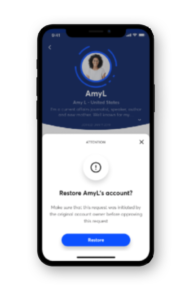
Layer 2 of the stack concerns how people can communicate directly with each other in a trustworthy way. This is made possible by using software “agents” installed in a digital wallet app on a phone to manage cryptographic keys and permissions.
Building on the DID infrastructure of Layer 1, the DID communication layer makes this communication secure by using standardized encryption and protocols. This common foundation allows agents to exchange information as allowed and requested by their owners.
Basically, the governance framework here must answer how people are going to trust wallets and agents. What are the considerations and requirements needed to ensure privacy and security so that messages can be passed securely between parties without observation?
Thus, what kind of governance framework is necessary for a:
- Hardware provider
- Software provider
- Agents
This layer must also handle digital guardianship (i.e., how can children or those who need a guardian to act on their behalf use this technology).
Again, all of this must be transparent and accessible.
Layer 3 concerns applications data exchange protocols—the different protocols used to issue a credential and to prove something to a verifier. The challenge here is how should a verifier make a decision whether to trust a credential? What’s the governance framework for establishing an authoritative credential or revoking it?
Therefore, the governance framework needs to establish rules and policies for
- Credential registries
- Authoritative issuers
- Insurers
Insurers are required to deal with risks entailed with an issuer making a mistake.
The ToIP envisages tens of thousands of different interoperable frameworks for different communities.
Layer 4 looks at the ecosystems that can emerge out of the previous three layers. Here credentials may be used in multiple ways in multiple places. An ecosystem might be an industry, an educational or health system.
Governance frameworks here must establish policies for:
- Member directories
- Auditors
- Auditing accreditors
This layer deals with the broadest layers of trust. For example, passports would be considered an ecosystem with a governance framework underpinning universal acceptance.
Takeaways
The ToIP Foundation has set itself an epic and an important task, and at Indicio.tech, we’re very excited to see how all these details are filled in and how they can be applied to our customer’s needs. Anything that advances trust and interoperability online has our support.
There is also the potential to standardize governance frameworks by including machine readable formats. This would benefit everyone.
We would emphasize one critical point. It’s easy to see all this as a challenge that technology companies can work out by themselves, as they are the ones closest to understanding the new technology and how it can be used. As a standards body, the ToIP Foundation needs to be proactively inclusive.
Identity concerns everyone. Governance of and trust in decentralized identity concerns everyone—and that includes women, people of color, marginalized communities, civil society organizations, and a wide array of experts who have thought deeply about identity outside of technology.
We all believe that decentralized identity is the path to creating a more trustworthy world. If Trust over IP is going to get us there, it must also mean trust from diversity.