Phishing attacks are all too common, and as a few casinos in Las Vegas are finding out, incredibly costly. As we continue to interact online, the only way to really stop these attacks is to have cryptographic confidence in who you are speaking with.
By Sam Curren
The MGM Grand recently made headlines for all the wrong reasons. A very public cyber attack wreaked havoc with slot machines, guests’ hotel room keys, and even elevators. For a brief summary, a group called Scattered Spider was believed to be using a Ransomware-as-a-Service (RaaS) made by BlackCat. RaaS is an ongoing issue, allowing even new and inexperienced would-be criminals access to sophisticated tools. What’s more interesting, however, is how they got in: a 10-minute call with IT.
According to the Cybersecurity and Infrastructure Security Agency (CISA), 90% of ransomware attacks begin with phishing. It is a massive problem in our ever-online world, and many groups are very good at appearing to be someone you already know. Even “advanced” security measures like multi-factor authentication have proven to be less than effective at stopping all attacks. We need something new. We need real confidence in who we are talking to.
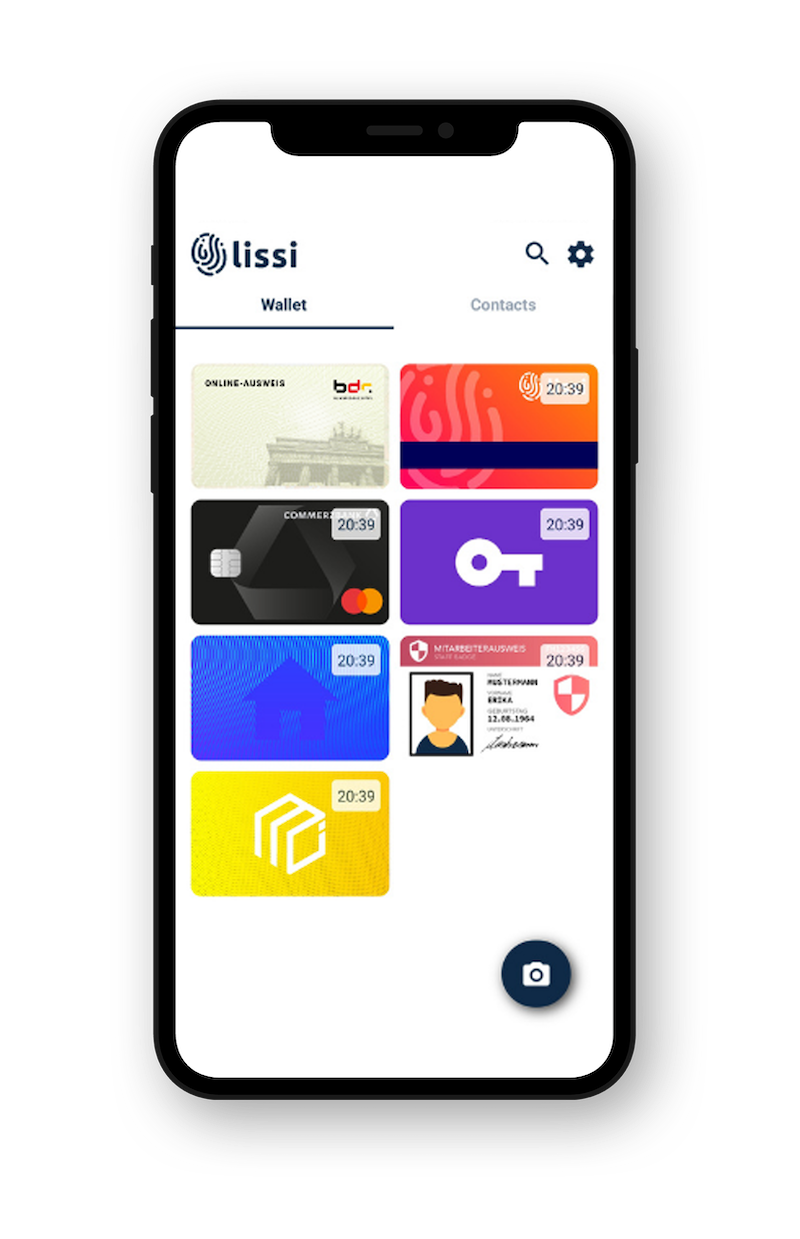
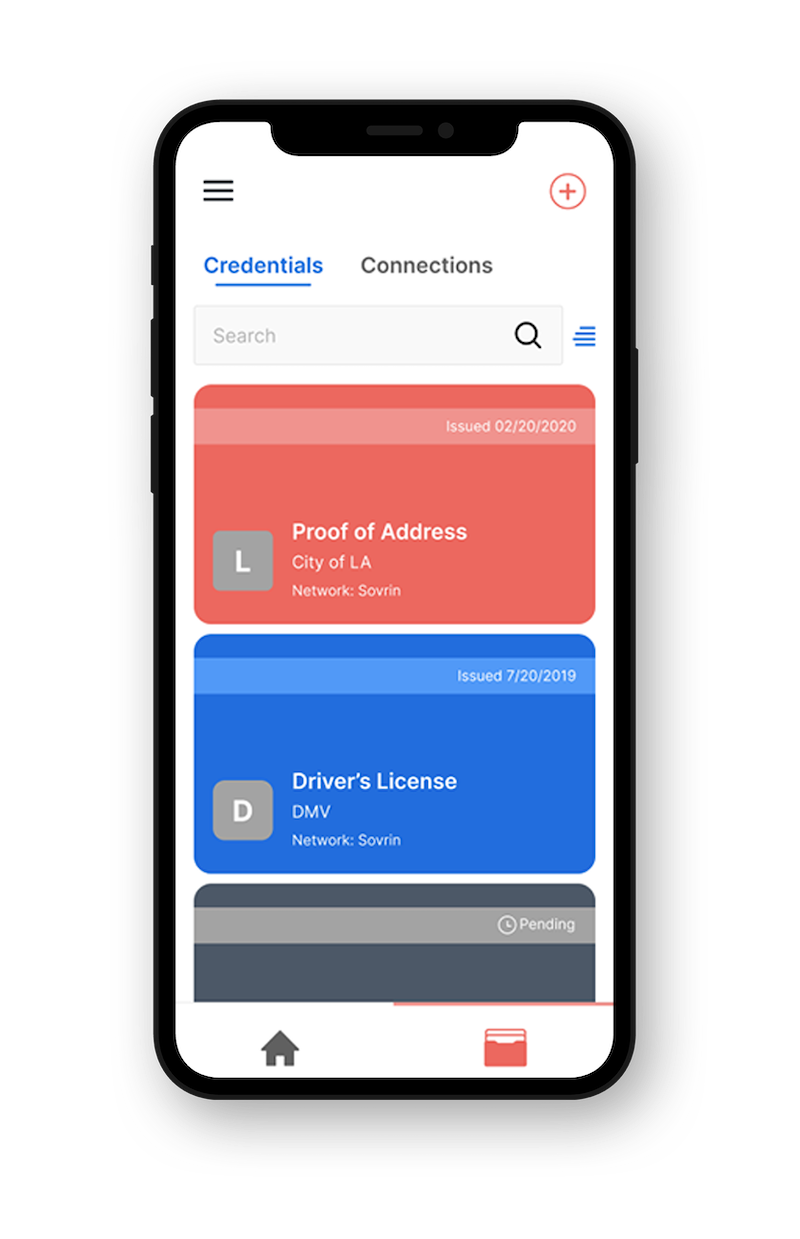
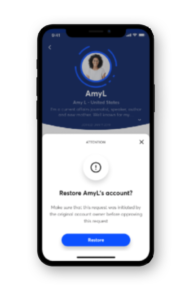
Verifiable credentials and DIDComm help establish this confidence. Unlike passwords and recovery questions / email recovery, verifiable credentials cannot be guessed, lost, stolen, or spoofed, and they can be presented to establish proof of identity, even on phone calls or chats.
These technologies accomplish this by providing a fundamentally different approach to the ones we have used in the past: Rather than granting access to an account or resource through a shared secret, such as a password, verifiable credentials, decentralized identifiers (DIDs) and DIDComm create a secure connection in which participants can mutually authenticate each other’s identity through cryptography before sharing any information.
By using verifiable credentials to manage access to critical systems, casino staff can use the secure connection created by DIDComm to confirm that the person they are talking to is, in fact, the person they claim to be. The verification takes place in parallel with the phone conversation and is much harder to attack. After verification, both parties on the phone call can now be confident in the identity of each other, in spite of the lack of security of the phone call itself. While no solution is fully attack-proof, this approach will yield substantially increased security and a reduction in phishing attacks.
These casinos have lost income, time, and most importantly, the trust of their consumers, because of their inability to securely verify the identity of the person on the other end of the line. Situations like this are reminders that even the biggest of organizations, with expensive security systems, have holes in their defenses. As long as you rely on a human knowing who they are speaking with as a part of your security strategy — whether it be the average employee or security professional — they are liable to be fooled. We have the technology now to have cryptographic certainty in who we are interacting with. It’s on us to start using it.
If you have any questions about these new tools we would be happy to discuss them with you. Please feel free to contact the Indicio team here.